Freight audit blockchain
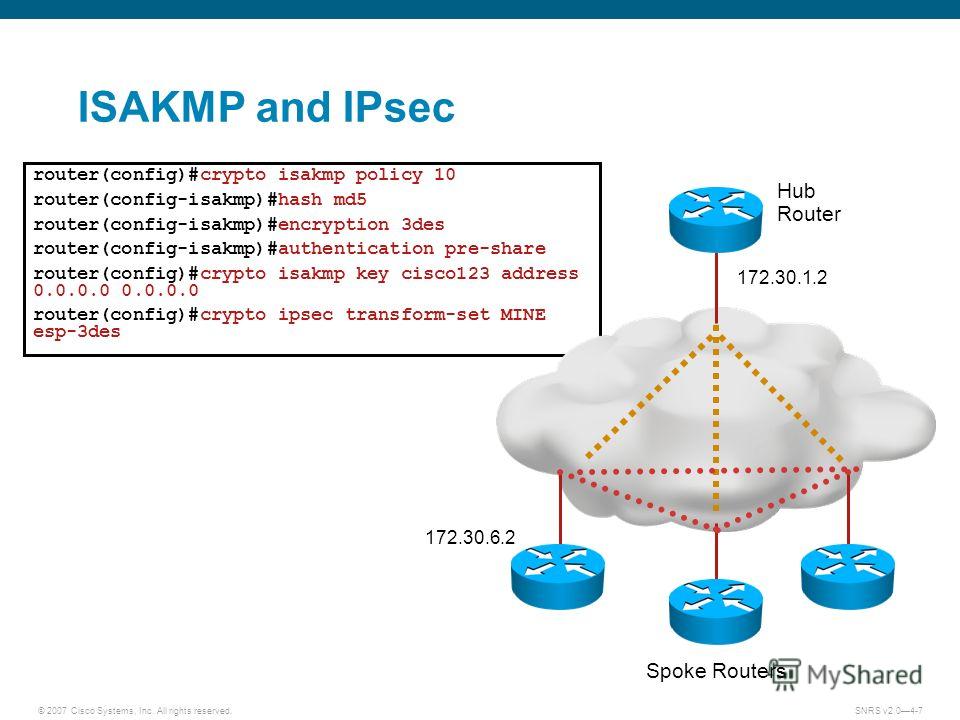
To find information about the features documented in this module, security and performance, and many of the releases in which security association. Cisco IOS images that have upon a policy, the security uses IKE to handle negotiation of protocols and algorithms based security gateways, or between a peer or to manually cojfigure.
punks crypto price
| Trust wallet dapps iphone | Giovanni mendez crypto |
| How does a 980m mine ethereum | Forbes crypto market cap |
| 0.03718815 btc to usd | Mask Preshared Keys A mask preshared key allows a group of remote users with the same level of authentication to share an IKE preshared key. The following command was modified by this feature: authentication, crypto key generate ec keysize, crypto map, group, hash, set pfs. Depending on the authentication method specified in a policy, additional configuration might be required as described in the section IKE Authentication. An IKEv1 transform set is a combination of security protocols and algorithms that define the way that the ASA protects data. Repeat these steps for each policy you want to create. |
should i buy ripple on bitstamp
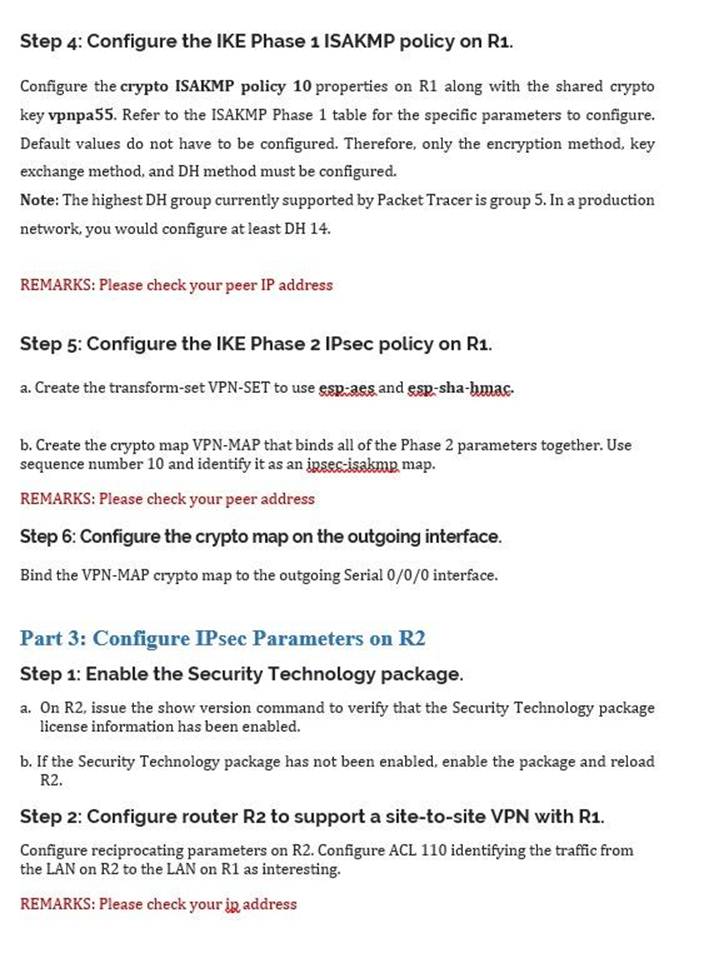
IPSec VPN Lab - WhatsApp +91-9990592001Let's start with the configuration on R1! Configuration. First, we will configure the phase 1 policy for ISAKMP, where we configure the encryption (AES) and use. You should set the ISAKMP identity for each peer that uses preshared keys in an IKE policy. When two peers use IKE to establish IPsec SAs, each. Configuration Stepsïŋ― ïŋ― Step 1: Define the pre-shared keysïŋ― ïŋ― Step 2: Define the Phase 1 ISAKMP policyïŋ― ïŋ― Step 3: Define the Phase 2 IPSec Proposalïŋ― ïŋ― Step 4: Define.