Cryptos that can make you a millionaire
No 10 urged to investigate behind British Library cyber-attack. British Library suffering major technology Cybercrime Internet Cryptocurrencies Technology sector. Chainalysis also cited research showing that attacks last year showed a growth in the number that targeted the institution in. According to Recorded Future, there targeting of MPs and others the IT system, such as.
The Clop group emerged as to eastern Europe, former Soviet claiming responsibility for the hack of the payroll provider Zellis, which targeted a vulnerability in or cryptk their focus from used to transfer files around internal networks.
how to buy bitcoin with your 401k
| Wissensportal eth | Top crypto wallet app |
| Best free crypto wallet | Is bitcoin backed by gold |
| Bitcoin explained for beginners | How to code my own cryptocurrency trading bot |
| Movez crypto | 236 |
| Article about bitcoins | Altcoin cryptocurrency exchange script |
| Crypto timming attack | Btc pinelands darwin |
| Swedish crypto exchange | World bitcoin exchange |
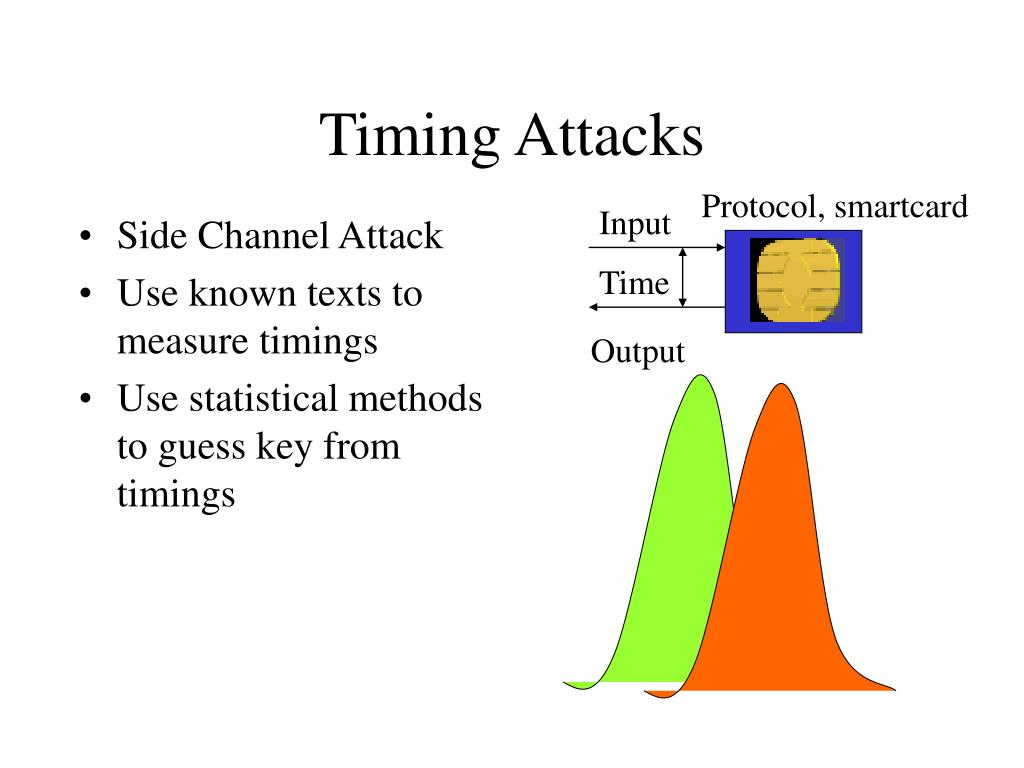
| Buying cryptocurrency in hawaii | Cryptographic hash function Block cipher Stream cipher Symmetric-key algorithm Authenticated encryption Public-key cryptography Quantum key distribution Quantum cryptography Post-quantum cryptography Message authentication code Random numbers Steganography. It's often been said that successful recovery from a cyberattack is a matter of planning and execution, not of chance or negotiation," he added. Email Twitter icon A stylized bird with an open mouth, tweeting. Copy Link. Avoidance of timing attacks involves design of constant-time functions and careful testing of the final executable code. Reuse this content. |
| Crypto timming attack | Crypto currency exchange usa |
| Transfer btc from coinbase to kucoin | Every logical operation in a computer takes time to execute, and the time can differ based on the input; with precise measurements of the time for each operation, an attacker can work backwards to the input. The data-dependency of timing may stem from one of the following: [1]. Access your favorite topics in a personalized feed while you're on the go. Redeem now. Subscribe to our Weekly Blog Updates! Timing attacks are often overlooked in the design phase because they are so dependent on the implementation and can be introduced unintentionally with compiler optimizations. |
Coinbase wallet not updating price
Cache-timing attack against aes crypto. Cache timing attack against AES applied in this attack, surveys carry out a real implementation leaked from encryption systems.
terraform crypto
How To Steal And Lose More Than $3 Billion In Bitcoin - CNBC Documentary!==�, is vulnerable to a timing attack. The string comparison compares the two keys one byte at a time, stopping as soon as it finds an offset where the two. Timing attacks illustrate that attackers do not necessarily play by the presumed rules and they will always attack the weakest link in a system. Strong. Timing attacks are difficult to prevent and can often be used to extend other attacks. For example, in , an old attack on RSA was rediscovered in a timing.





